They did not stumble into this. Every move was planned, every wallet pre-selected, every transfer timed to the second.
As investigators peel back the layers of what is now one of the most sophisticated bank heists in East Africa’s recent history, the picture that emerges is not of opportunistic thieves grabbing what they can find.
It is of a disciplined criminal enterprise that had studied its target for months, tested its limits methodically, and coordinated its escape with surgical precision. The logs prove it. The chat messages prove it. The timestamps prove it.
This is Part 3 of Inside the Equity Bank Heist — and this time, we know considerably more about who these people are, how they operated, and why some very important questions are still waiting for answers.
The Architecture of a Criminal Network
Start at the top, because that is where the instructions came from.
Somewhere in Canada sits a Nigerian man known in Signal chats only as “HK.” He did not fly to Kigali or plant any device. What he did — and this is what makes him arguably the most significant figure in the entire operation — was to think, delegate.
He told the team on the ground not to use laptops. Use Raspberry Pi devices instead. Small, silent, the size of a credit card, cheap enough to be disposable, and invisible once placed inside a corporate network.
That single instruction fundamentally shaped the method of attack. HK remains at large.
Below him, in Kenya, is the person investigators are calling Carmen — a second-in-command currently on bail. Sources describe that bail as dubious, and the unease is shared among investigators watching someone at that level of the operation move freely while the case is still being built.
Third in the known hierarchy is a Ugandan referred to as Daglous — number three in the chain of command, positioned between the strategic leadership and the operational ground team.
Then come the people whose names, phones, laptops, and hard disks are now spread across forensic examination tables.
Enock Mpanga: The Engineer
Enock Mpanga is the primary technical suspect, and the forensic evidence found on his devices reads like a project plan for a corporate network infiltration.
His laptop was set up on September 4th, 2025 — more than five months before the fraud.
From the beginning, the timezone was configured to East Africa, and investigators noted possible use of the TOR browser for discreet access. By January 4th, 2026, Enock was messaging via Signal, asking whether “the Equity guys were serious” — waiting for the Raspberry Pi to arrive so it could be sent to “the other party.” Configurations were needed before proceeding, he said.
The procurement records on his laptop tell a story of scale and deliberate planning. A purchase order dated February 2nd, 2026, documents a request for 35 Raspberry Pi 5 devices with associated accessories.
The billing details reference Hillsborough County Schools in Tampa, Florida — a school district used as institutional cover. The shipping contact is listed as Simon Lubwama, a Ugandan national whose passport copy was also found on the same laptop. A second order dated January 31st shows another 35 units.
A third order from PiShop US, bearing the subject line “thank you SIMON,” covers 35 more Raspberry Pi 5 devices with 16GB RAM. Altogether, more than a hundred compact, configurable computers, ordered in batches, using institutional cover, shipped to a Ugandan national in the United States.
Raspberry Pi devices come without an operating system — the end user installs one. On Enock’s laptop, investigators found Kali Linux version 2025.3, a security-testing operating system favoured by penetration testers and, less legitimately, by people who want to probe and exploit networks.
They also found Rufus, the tool used to flash operating systems onto bootable media. The Raspberry Pi, loaded with Kali Linux, configured for the bank’s internal proxy settings, and slipped quietly into the ex-Coge network — that was the plan.
An insider at Equity Bank Rwanda was consulted via KDDD about whether the device would bypass Cisco Network Access Control. Enock’s response was confident: the Pi device will not have an issue.
Signal chats from Enock’s laptop show him discussing the operation with a contact whose messages reference “Equity en 211” — a coded phrase that turned out to mean Centenary Bank, a licensed commercial bank in Uganda, suggesting parallel cross-border banking ambitions. Another screenshot shows a conversation with a contact saved as “Kristian,” discussing Rwanda and “getting more accounts” in Zambia.
This network was thinking regionally from the start.
Enock also showed the operational security awareness of someone with experience.
He cleaned up his browser profiles on the morning of February 18th and again on the evening of February 26th — both after Equity Bank’s team had begun frustrating the fraud. But he did not clean everything.
On his desktop, investigators found a file whose name was formatted to closely mimic the legitimate Equity Online banking URL. Inside it: the login credentials, debit card details, and CVV of a customer named Eric Ikorukwishaka. Also on the laptop was Eric’s full account statement, downloaded at 4:02 in the morning, East Africa Time.
The level of detail suggests either very sophisticated access or very willing cooperation from the account holder.
Enock’s prior history with law enforcement is also on record. WhatsApp chats from 2018, recovered from his laptop, reference a laptop seized by Wandegeya Police Station in Kampala and three active court cases. A media article about a tax evasion case before Uganda’s Anti-Corruption Division of the High Court was also saved on his device.
This was not his first encounter with investigators.
Solomon Mugisha: The Coordinator
Solomon Mugisha ran the communications. He is “KDDD” in the chat logs — a handle that appears throughout the Signal exchanges on Enock’s devices and on Solomon’s own iPhone 15 Pro Max.
On February 11th, 2026, Solomon shared a list of web hosts in a file called ECW-20hosts.xlsx with a contact operating as “katempalexis,” asking the IT person behind that handle to check for network mapping opportunities or web API access points. On February 14th, as the operation went live, Solomon received a query about two specific internal IP addresses — 172.31.21.206 and 172.31.27.133 — from katempalexis.
He screenshotted the message and forwarded it to “Jose Lopez,” who confirmed access to both. Later, Jose Lopez reported that he had found many web hosts but nothing useful — the ex-Coge web API remained out of reach for that team. But Enock’s team was already inside through a different route entirely.
By February 15th, Solomon was pushing hard. He pressurised Enock via Signal to use “the ki machine” and get the money moving. “React faster,” he insisted, confirming he had already told “the guy” that they had received the beneficiary lines.
asked for patience. Solomon replied that they needed to keep making money.
Among the account numbers Solomon directed funds to was 4007211347993, belonging to Nziza Julius, positioned near the Mirama Hills border post in Ntungamo, Uganda. “It will not trace back,” the message says — acknowledging in the same breath that it was risky.
The border was the exit point. Once cash crossed into Uganda, the trail cooled.
Solomon’s phone also held cryptocurrency wallet screenshots. A 6,800 USDT transfer on December 11th. A 17,500 USDT transfer on December 12th. A 13,980 USDT transfer and a Bitcoin transaction on December 16th. The wallets carried minimal transaction history — consistent with accounts prepared and waiting to receive a large injection of laundered funds.
As of the report date, they had not been used for that purpose in connection with this incident. But they existed, and they were ready.
Kayimba Farouk: The Man Who Knew Before It Happened
Kayimba Farouk knew the attack was coming. That is not inference — it is in the chat records. On February 6th, more than a week before the first fraudulent transaction, he told an unknown cash mule that the cash-out from Equity Bank Rwanda would happen on the weekend of February 14th. He did not guess. He knew because he was part of the planning.
When the transfers began, Kayimba was ready. He had access to the account of a customer named Divine Ishimwe — opened on February 10th, just four days before the fraud. Between February 14th and 15th, that account received Rwf 138,920,000.
Every franc was withdrawn via MTN MoMo and ATM cash withdrawals at machines in Kampala, Uganda. One screenshot recovered from Kayimba’s Huawei Honor 200 Pro shows him accessing Divine Ishimwe’s account in real time on February 15th.
WhatsApp messages from February 13th show him and a contact called “Saint” exchanging mobile numbers — the lines to which money would be sent later that night. By February 17th, Kayimba was still coordinating withdrawals, discussing agent locations, withdrawal share arrangements, and operations inside Uganda.
He also moved funds through Chipper Cash, the cross-border neobank popular across Africa, routing money through a platform designed for exactly the kind of low-friction, multi-currency transfers that complicate forensic tracing.
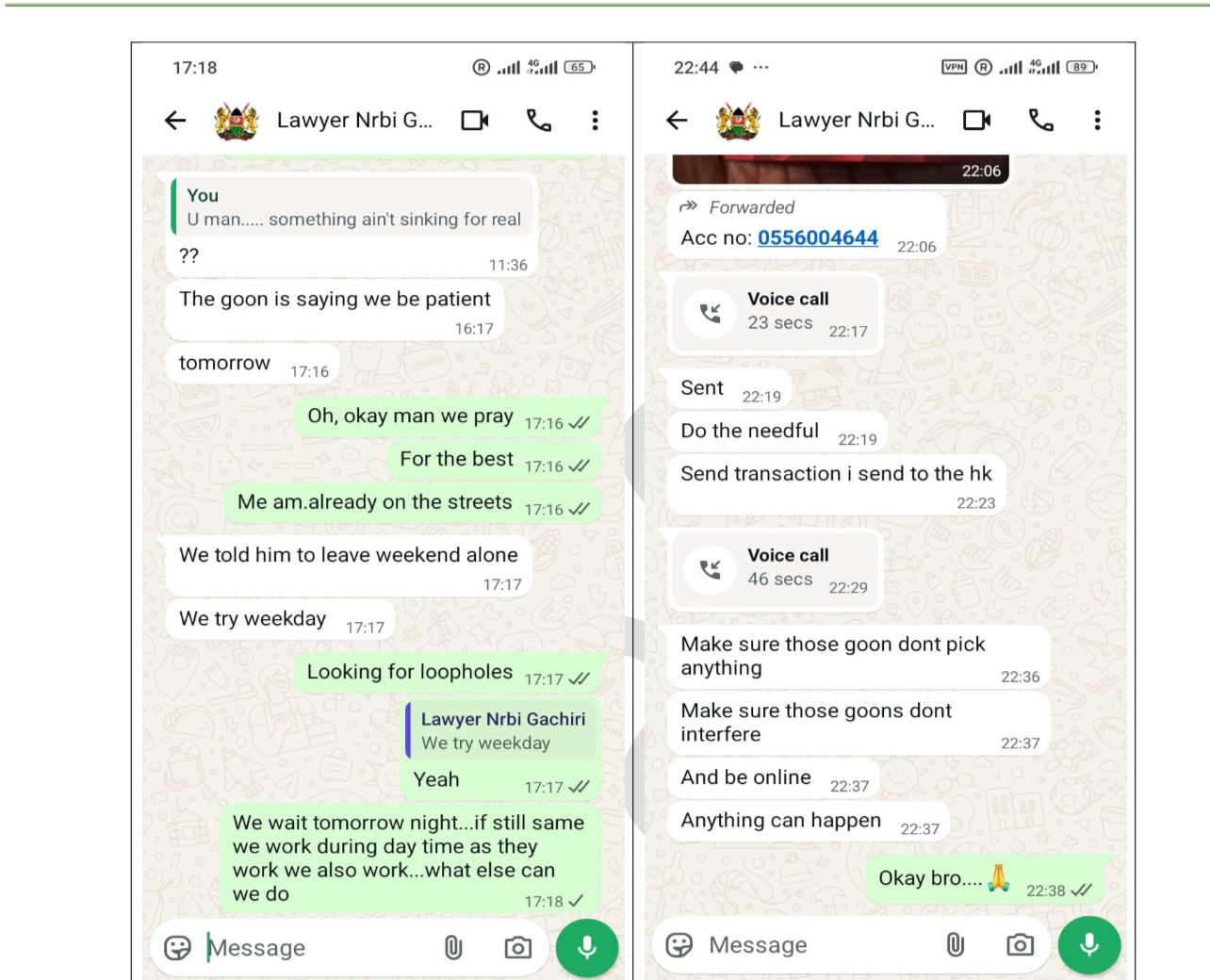
His Kenyan contact “Lawyer Nrbi Gachiri” supplied Safaricom SIM lines for the Kenyan end of the withdrawal infrastructure.
Katamba Ismail: The Identity Architect
Nine phones. Investigators seized and examined all of them. Most yielded nothing. But one device — a Tecno Pop 10C — told a precise and disturbing story.
On February 20th, 2026, at 2:33 in the afternoon, Katamba used that phone to photograph a newly opened Equity Bank Uganda account in the name of Keezi Eliphaz Kazana: national ID, Visa debit card number, NIN — everything. At 3:53 that same afternoon, from the same device, he created the Gmail address martineliphaz2@gmail.com, screenshotted the password, and saved it.
Keezi Eliphaz Kazana’s entire financial identity had been absorbed into the network, ready to be used by someone else.
The Contract Cancelled: Innocent Kaneza and the Esicia Question
Of all the threads investigators are now pulling, perhaps none is more consequential — or more sensitive — than the one leading to Esicia Ltd and its chief executive, Innocent Kaneza.
Esicia was the technology vendor that built, maintained, and held administrative access to CogePay — the internet banking platform at the heart of the fraud. Their VPN server, at IP address 10.22.97.60, was used to access Equity Bank Rwanda’s internet banking servers on February 9th and again on February 16th.
On February 9th, there was access to the application and database server and into the CogePay database via phpMyAdmin — the web tool used for database management. There was no support ticket, no approved task, no request from the bank.
The access simply happened. On February 16th — the day the fraud was discovered — someone logged back in from the same VPN server and deleted critical log files covering the period from February 9th to 10am that morning.
The forensic report is careful with its language. It notes that because Esicia owns the credentials to the VPN server, the logins could be attributed to Esicia staff — or to anyone else who may have accessed those credentials. That is a window, not a conclusion. But it is a window that points directly at the vendor.
Beyond the access and deletions, investigators found malicious files on the CogePay servers that predate the fraud by months.
A Metasploit Mettle payload capable of providing remote access, dated October 3rd, 2025. An encoded web shell dated October 4th, 2025. Another web shell dated January 13th, 2026.
A reverse shell with a hard-coded external IP address, dated December 30th, 2025. The database password was stored in plaintext in the system configuration — described in the forensic report as “an insecure configuration available for exploitation.”
This was not a smash-and-grab. Someone had been inside the system for months before a single fraudulent transaction was processed.
Equity Bank Rwanda has since cancelled its contract with Esicia. Innocent Kaneza told Taarifa he could not comment. What he could not do, according to sources, was explain to the bank how his platform had been used as the primary vehicle to penetrate and defraud it. That is not a peripheral question. It is the central one.
A vendor who manages a financial platform and cannot account for how it was compromised — cannot explain the unauthorised access, cannot explain the log deletions, cannot explain months of dormant malware sitting on his servers — is a vendor whose relationship with this investigation deserves very close attention.
There is one more detail that investigators have noted quietly. At the time of the heist — the weekend of February 14th to 16th — Innocent Kaneza was in Nairobi, Kenya. Nairobi is, coincidentally, the city where Carmen, the Kenyan second-in-command of the fraud ring, is based and where he is currently on dubious bail. Whether Kaneza’s presence in Nairobi at that precise moment carries investigative significance is a question that has not been publicly answered. But it is a question that investigators are asking.
Louis Bizimana: The Staff Member With Questions to Answer
On February 9th, 2026 — five days before the first fraudulent transaction — a laptop registered to Louis Bizimana, a software developer in Equity Bank Rwanda’s IT department, connected to both the Esicia VPN server and the CogePay application and database server. He had no approved task on either system that day. No support ticket. No work order.
CrowdStrike endpoint detection logs and LogRhythm SIEM logs both captured the connection clearly, showing Louis’s device browsing CogePay web resources on the application server.
But when investigators checked the CogePay admin portal server logs to corroborate the activity, the records were not there. His activities had been deleted. And that deletion, the forensic report states, could only have been performed using administrative database accounts exclusively in the custody of Esicia Ltd.
Louis’s laptop also contained stored credentials for both the Esicia VPN server and the CogePay portal — an arrangement the bank had no knowledge of. A software developer at the bank, holding the vendor’s VPN credentials, connecting to restricted servers on a day no work was authorised, whose tracks were then erased using the vendor’s own administrative tools. Each of those facts, individually, raises questions. Together, they demand answers.
Eric Ikorukwishaka: The Customer Who Chose to Help
Eric Ikorukwishaka is not a hacker. He is an Equity Bank Rwanda customer who made a choice. He shared his Equity Online login credentials, his debit card number, his CVV, and validated OTPs sent to his own phone number, 250796906782.
On February 14th, Rwf 7.5 million landed in his account from BRALIRWA via CogePay. Within hours it was moving again: Rwf 1.5 million to Patrick Tuyizer, Rwf 500,000 to Amos Iradukunda, and the remainder to other accounts and wallets, including one belonging to a company called TANGIMPUNDU Ltd. His account was a transit point, not a destination. How much he kept for his role is still being established.
The Four People Who Were Used Without Consent
Four names from BRALIRWA’s CogePay account deserve to be read very differently from everyone else in this story: Gloriose Mamashenge, Dusenge Lydia, Manzi, and Katell. These were legitimate BRALIRWA employees whose credentials were stolen, whose passwords were reset in the dead of night, and whose accounts were used to authorise transactions they knew nothing about.
Password was reset at 3:24 in the morning on February 14th. The new password — “ed6a7p” — was sent via SMS to a phone number she did not control: 250794045257. That number had been configured across fourteen separate BRALIRWA user accounts on the CogePay platform, meaning a single SIM card holder could receive authentication codes for fourteen different employees simultaneously.
Whoever held that SIM held the keys to everything.
The reset was performed from a Linux desktop device — identified by its browser signature as Mozilla/5.0 (X11; Linux x86_64) — connected from inside the CogePay application server.
The same device had been actively navigating the portal’s internal pages, pulling reports, and submitting login requests in the minutes immediately before the password change. This was not automated scanning. It was an interactive human session inside a bank’s salary disbursement system.
What followed was almost clinical. Each of the nine traceable transactions follows an identical sequence, timestamped to the second: Gloriose initiates a bulk transfer, Lydia verifies, Manzi attempts to sign, Katell completes the signing. All using OTPs delivered to the number the attackers controlled. All within minutes of each other, across a single day, starting just after 11am and running past midnight.
The configuration that made this possible should never have existed. All sixteen BRALIRWA user accounts on CogePay were set to receive OTPs through a single shared email address — charles.niyitegeka@heineken.com — while fourteen of those accounts also shared the same mobile number. That is not a security architecture. That is a single point of catastrophic failure, dressed up as a configuration choice.
The Money’s Journey: 453 Transactions, 301 Numbers, Rwf 1.359 Billion
Once the money left Equity Bank, it moved fast and it moved wide.
A tentative spreadsheet titled “Fraudulent Float Purchase” has become one of the investigation’s most revealing documents. It records 453 transactions totalling Rwf 1.359 billion, sent to 301 unique phone numbers linked to approximately 369 names. The overwhelming majority appear to follow Rwandan naming patterns, with a smaller number suggesting regional East African origins.
The internal structure of those transfers is what makes experienced fraud investigators pause. Of the 301 phone numbers, 101 received money more than once — accounting for 253 of the 453 total transactions. More than half of all payments went to a tenth of the recipients.
That is not random. It is a managed distribution: a pre-arranged pool of trusted wallets recycled to absorb and move large sums.
One number — 250796909838 — received Rwf 71.97 million across just two transfers, the highest single total in the dataset. Yet it is recorded as “Not appearing on MOMO.” That anomaly remains unexplained. Whether the account was removed from visible records after the fact, routed through an unusual channel, or linked to records that were interfered with, investigators are still working to establish.
A recipient associated with the name Fabrice Hirwa received nearly Rwf 39 million across three separate payments. Several others received between Rwf 10 million and Rwf 16 million through repeated transfers. At those volumes, these were not passive end recipients. They were operational nodes — collection points or redistribution hubs within a coordinated withdrawal network.
 Meanwhile, many other payments were clustered in smaller, rounder amounts: Rwf 2.5 million, Rwf 3 million, Rwf 4 million. That is structuring — the deliberate splitting of large sums into smaller transfers to avoid triggering alerts, breaching wallet limits, or crossing compliance thresholds. Whoever designed the payout schedule knew precisely how the mobile money system’s parameters worked and calibrated every transfer accordingly.
Meanwhile, many other payments were clustered in smaller, rounder amounts: Rwf 2.5 million, Rwf 3 million, Rwf 4 million. That is structuring — the deliberate splitting of large sums into smaller transfers to avoid triggering alerts, breaching wallet limits, or crossing compliance thresholds. Whoever designed the payout schedule knew precisely how the mobile money system’s parameters worked and calibrated every transfer accordingly.
Preliminary profiling suggests many of the linked identities appear to be under thirty years of age — a young, digitally fluent network comfortable moving money at speed across platforms and borders.
The strategic logic of spreading funds across 301 numbers is not accidental either. A single freeze order cannot stop three hundred threads simultaneously. By the time investigators had mapped the full distribution, a significant portion of the money had already been withdrawn, converted, or moved onward across borders.
Hannington Namara Moves
Equity Bank Rwanda Managing Director Hannington Namara has not been managing this crisis from behind closed doors. On Monday, he sat down with MTN Rwanda’s chief executive,Monzer Ali, for a technical and strategic conversation — direct, frank, and focused on what must happen next.
The two institutions are now jointly engaging with RIB and other relevant bodies to pursue accountability for the more than four hundred Rwandans whose phone numbers appear in the transfer records.
On its own side, Equity Bank has moved decisively. Namara confirmed that the bank has significantly tightened controls, including a mandatory restriction: no account can now process a withdrawal exceeding Rwf 10 million without direct human interaction between the bank and the customer.
Not a digital token. Not an OTP sent to a number shared among sixteen people. A real conversation. That single control, had it existed before February 14th, might have stopped much of what followed.
The cancellation of the Esicia contract is part of the same internal reckoning.
The vendor relationship that granted a third party administrative access to core banking infrastructure — access that was apparently shared informally, operated outside official channels, and used to delete critical evidence — has been terminated.
The Regulatory Gap Nobody Wants to Name
Here is where the investigation reaches its most uncomfortable territory.
There are active deliberations about whether the National Bank of Rwanda should take formal action regarding MTN MoMo Rwanda — examining whether the episode reflects regulatory non-compliance or a systemic oversight failure that allowed cross-border cash withdrawals of this scale to proceed without intervention.
The concern is fundamental: a standard individual MoMo wallet is a personal financial instrument, not a licensed mobile money agent account with full KYC infrastructure and commercial-volume transaction monitoring.
Yet in the days following the fraud, individual wallets were used to extract hundreds of millions of francs out of Rwanda — across borders, at a velocity that should have triggered every alert in the system.
RURA was engaged and asked to produce a detailed report on each SIM card’s registration, KYC documentation, and transaction history during the relevant period.
That is the bedrock of any serious accountability exercise. The National Bank of Rwanda’s posture, however, has been a different matter. Sources say the central bank took an early and premature position that the incident was purely the bank’s responsibility — and having taken that position, it effectively stopped looking for the systemic failures that cut across the entire financial ecosystem.
It has not shared information with nor actively facilitated the investigation in the manner expected of a regulator during a cross-institutional fraud event of this magnitude.
That stance is being pushed back on. Because what the data shows is not a story about one bank’s failure. It is a story about a system whose collective gaps were studied, mapped, and exploited by people who knew exactly what they were looking for. The institutions not currently sharing accountability for those gaps will, eventually, need to explain why.
Over four hundred Rwandans received money from this operation. Their numbers are documented. Their accounts received the transfers. Some almost certainly knew what they were receiving and why.
Others may have been unwitting participants — handed a SIM card, told to keep a wallet open, asked no questions they chose to answer honestly. But the money is traceable.
The numbers are known. And the question that sits at the centre of this entire investigation — why have these people not been compelled to return what they received — does not yet have a satisfactory answer.
Convergence
Some suspects have been released since their arrest. Carmen is on bail in Nairobi. HK is in Canada. Daglous remains in the picture. The investigation spans at least four countries and multiple regulatory jurisdictions, and cross-border coordination in cases like this is never fast or clean.
And yet, people tracking the investigation describe a mood not of stagnation but of gathering momentum. The separate threads — digital forensics, phone records, bank transaction logs, SIM card data, the float purchase spreadsheet, Esicia server access logs, Signal chats, the Raspberry Pi procurement trail — are moving toward each other.
Investigators across agencies are approaching convergence: the point at which the individual findings stop being separate puzzles and begin forming a single, coherent, prosecutable picture.
The people who designed this heist were not careless. They deleted logs.
They planted hardware months in advance. They communicated on encrypted platforms. They split a billion-franc theft across hundreds of wallets.
They operated across borders with the confidence of people who had either done this before or studied it closely enough to know the playbook. Enock’s 2018 court cases suggest the former.
Catching them — and making them genuinely pay — will require institutions that can match that coordination with cooperation, transparency, and urgency. That alignment is still being built. But it is being built. And the walls, slowly but unmistakably, are closing in.
This is Part 3 of an ongoing investigative series. Further reporting will follow as the investigation develops.
Inside the equity bank heist (part 2): The Mobile Money Trail, Third Parties And The Billions That Moved ☞ https://taarifa.rw/2026/04/18/inside-the-equity-bank-heist-part-2-the-mobile-money-trail-third-parties-and-the-billions-that-moved/